Dear Sentinels
Last week I joked about spring finally arriving, and while it’s still dragging its feet, at least it’s starting to feel a bit warmer. Anyway, we’re back on our Zero Trust journey this week, but this time we’re getting into the nitty-gritty of actually putting it into practice. In the academic article, we’ll dig into why, despite what most people think, rolling out a Zero Trust system can actually be cheaper than sticking with the old ways. And yes, we’re circling back to the Flipper Zero as well, now running the shiny new Monument Firmware.
If you remember, last week I mentioned trying (and failing) to get a new ad up and running. Good news is that all stored out now:
Sponsored
The Privacy Design Lab
Fiedldnotes by the Privacy Design Lab is an education-first newsletter for leaders and teams who know the what and the why about data privacy but want to dig into the how. Practical privacy discuss...
Now, let’s dive into news from around the web, the Flipper Zero, our investigative piece, and the academic article review.
News from around the web
Every headline satisfies an opinion. Except ours.
Remember when the news was about what happened, not how to feel about it? 1440's Daily Digest is bringing that back. Every morning, they sift through 100+ sources to deliver a concise, unbiased briefing — no pundits, no paywalls, no politics. Just the facts, all in five minutes. For free.
To the Flipper Zero we go!
We’re going to install some new firmware, which is basically the board’s Operating System, just a bit more low-level. This one’s called Momentum, and you can find it here. It’ll look something like this:
And this is what it looks like to install the firmware:
Just plug in the Filler Zero and click install. Then, when it is installed, go to this site https://github.com/skizzophrenic/Ubers-SD-Files. Copy or git clone it to your computer, then either plug your Flipper into your computer or remove the SD card from the Flipper and plug it into a USB card reader. This latter option will be smoother than the previous deal. You can see all the options discussed in this video. If you have the special WiFi dev board, you can add a little bit more to it. Just watch the video to see how to flash your dev board with momentum. This will, for instance, let you de-authenticate any two connected devices on your own network. Then get PCAP files onto your SD card, and then export them onto your PC to investigate with something like Wireshark. But again, never ever de-authenticate any network that you don't have access to, never be a skid!
The Technologies Behind the Theory
These days, the old idea of a security perimeter is pretty much gone. Instead, we’ve got Zero Trust, where nobody and nothing gets a free pass, no matter where they are. At its core, Zero Trust is all about three things: the user, the resource they want, and a smart middle layer that decides who gets in. This middle bit is called the Policy Decision and Enforcement Point, and it’s basically the brains of the operation, checking in real time if someone should get access to an app or some data. To make all this work in the real world, companies have to match these ideas up with actual tech and products they’re already using.
The Policy Enforcement Point, or PEP, is basically the bouncer standing right next to whatever you’re trying to protect. The closer it is, the less chance there is for attackers to sneak around. Usually, this job goes to Next-Gen Firewalls like Fortinet or Palo Alto, which check traffic as it comes in. For a lighter touch, some companies use Software-Defined Perimeter gateways like Zscaler or Netskope, or Network Access Control tools like Cisco ISE or Forescout. And if you’re locking things down inside a data centre, micro-segmentation tools like Illumio or Cisco Secure Workload step in to keep servers from chatting with each other when they shouldn’t.
Complementing the enforcement layer is the Policy Decision Point (PDP), the “brains” that evaluates dynamic signals and risk before instructing the PEP to allow or block access. These decision engines are often integrated into Secure Access Service Edge (SASE) controllers from vendors like Zscaler, Cloudflare One, or FortiSASE, though purpose-built solutions such as StrongDM and Google’s BeyondCorp also perform this function. For a PDP to make informed decisions, it must ingest telemetry from a variety of sources. Identity Providers like Okta or Entra ID verify user credentials, while endpoint protection platforms such as CrowdStrike Falcon, Microsoft Defender, and SentinelOne provide critical data on device health and security posture. Furthermore, SIEM platforms like Splunk, QRadar, or Elastic Security contribute broader threat intelligence by aggregating logs to detect suspicious behaviour across the entire environment.
At the centre of this ecosystem is the Zero Trust Exchange, a cloud-native proxy solution designed to securely connect users to applications without ever placing them on the actual network. This process begins at the user’s device through the Zscaler Client Connector (ZCC), a single, lightweight application that manages all security modules. When a user attempts to access a resource, the app automatically finds the nearest of approximately 160 global Points of Presence (POPs) to ensure low latency and high performance. Before any traffic is forwarded, the system integrates with an Identity Provider like Entra ID to authenticate the user and evaluate conditional access policies.
Once identity is verified you’re in, the Zero Trust Exchange does its thing using two main tools. Zscaler Internet Access (ZIA) handles anything going out to the public internet or SaaS apps like Microsoft 365 or Salesforce. If you’re heading somewhere sketchy, ZIA can use Cloud Browser Isolation, which basically streams just the pixels to your browser so nothing nasty can run on your device. Meanwhile, Zscaler Private Access (ZPA) lets you access internal apps, whether they’re in the cloud or in your own data centre. Unlike old-school VPNs that open up your whole network, ZPA connects from the inside out using a tiny virtual appliance, so your private stuff stays hidden from the outside world, with advanced security layers such as Data Loss Prevention (DLP) and Firewall as a Service.
These features use deep packet inspection on encrypted traffic to stop unauthorised movement of sensitive data, whether it is moving or stored in the cloud. For users on unmanaged or Bring Your Own Devices (BYOD) who cannot install the client app, Browser-Based Access (BBA) solutions like the User Portal and Privileged Remote Access offer secure, clientless access to web apps and admin protocols such as RDP or SSH. Zscaler Digital Experience (ZDX) checks endpoint health and the network path, helping administrators spot and fix performance issues before they impact productivity. This all-in-one approach lowers the attack surface and removes the need for complicated legacy products.
The NIST framework can be found here.
Summary
The Zero Trust security model offers a comprehensive framework for safeguarding sensitive data by moving away from traditional network perimeters and instead implementing granular, continuous inspection of all digital business traffic. This report outlines eight key business and security benefits of the Zero Trust approach, highlighting its effectiveness in mitigating contemporary cyberattacks while supporting organisational growth and digital transformation.
“Zero Trust gives you unprecedented visibility into your digital business, from network packets to applications.”
Background
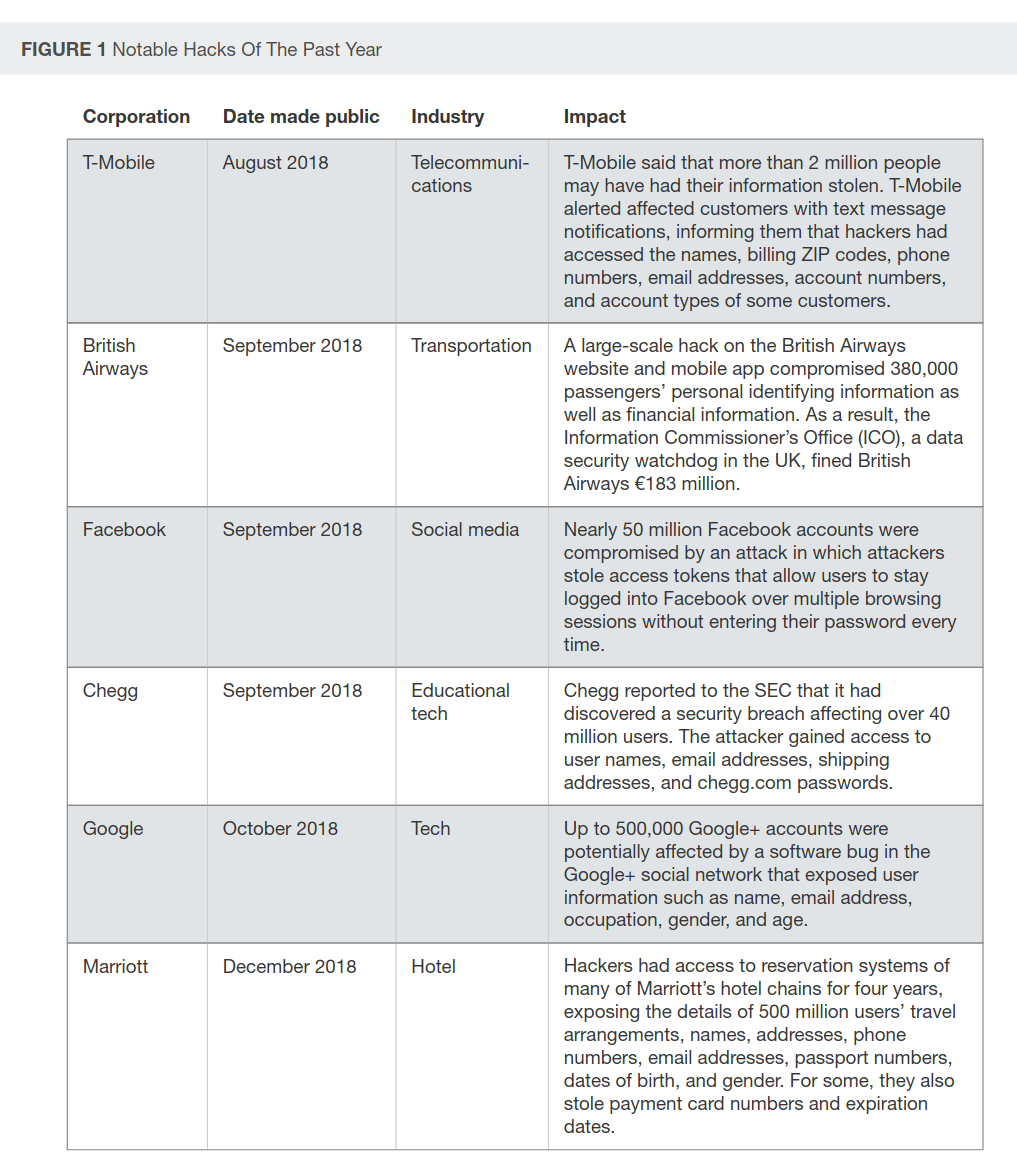
Traditional security infrastructures have become less effective due to their reliance on outdated perimeter-based models, which are inadequate for addressing the complexity of modern cyberattacks and the rapid adoption of cloud technologies. High-profile breaches at organisations such as Equifax and Capital One illustrate that security failures can result in substantial financial losses, executive turnover, and significant reputational harm. These incidents highlight the increasing importance of security outcomes for business sustainability and revenue protection amid persistent threats.

Security professionals frequently allocate significant resources to detailed network management, sometimes at the expense of the overarching objective of customer protection and business enablement. The Zero Trust model addresses this challenge by enabling both comprehensive data inspection and streamlined operations, capabilities that were previously viewed as incompatible within traditional hierarchical network structures. By evolving security architectures to accommodate new user groups and Internet of Things (IoT) devices, organisations can achieve a more resilient, next-generation security posture.
“Traditionally, the security team had no active role in conversations about organizational sustainability, revenue, profits, and executive competence.”
Use-case
A primary use case for Zero Trust is enhancing network visibility and breach detection by segmenting networks into microperimeters, thereby positioning security controls close to sensitive data. This architecture enables security teams to inspect all traffic at the application layer, facilitating rapid containment of malware and minimising the impact of intrusions compared to traditional networks. Additionally, Zero Trust supports vulnerability management by isolating areas of concern, enabling more targeted, effective patching strategies.
The Zero Trust model is also integral to digital business transformation and the secure integration of Internet of Things (IoT) devices. By using explicit permissions and microsegmentation, security professionals can connect a wide range of devices, such as medical imaging systems and point-of-sale terminals, without exposing the broader corporate network to threats. This approach positions the security team as a strategic business partner that enhances organisational agility, rather than serving solely as a restrictive guardian of a static perimeter.
“Zero Trust allows security pros to… become a partner in digital transformation.”
Conclusion
Future security architectures will focus on “inside-out” designs that optimise for flexibility and cost-effectiveness by integrating connectivity and transport around potentially toxic data. The report highlights significant cost reductions achieved by consolidating disparate security controls into single platforms, such as Next-Generation Firewalls (NGFWs), thereby lowering capital expenditures. Furthermore, Zero Trust reduces operational costs by centralising management consoles and narrowing the scope and cost of compliance initiatives like PCI DSS through inherent network segmentation.
“This translates into significant cost savings as multiple security controls are brought together into a single virtual or physical appliance.”
The report can be found here.


