Dear Sentinels
Wow, our third week already! This week, I am going to switch it up by talking about Cybersecurity. I meant to do this last week already, but then I found this resource of foundational papers on AI, and I got hooked. I do know this strong pull for me to investigate only the new thing in front of me, and yes, I know it's not conducive, but I do try. Ultimately though, it's like my friend says "great things from small beginnings".
So in this week's article, I will be looking at the UK National Cyber Security Centre's (NCSC) free cyber toolkit. Although it is intended for small businesses, it can also be used for individual Cybersecurity. And last but not least, we will turn our gaze out onto the heavens, or at least as high as the satellites fly...
Effortless Tutorial Video Creation with Guidde
Transform your team’s static training materials into dynamic, engaging video guides with Guidde.
Here’s what you’ll love about Guidde:
1️⃣ Easy to Create: Turn PDFs or manuals into stunning video tutorials with a single click.
2️⃣ Easy to Update: Update video content in seconds to keep your training materials relevant.
3️⃣ Easy to Localize: Generate multilingual guides to ensure accessibility for global teams.
Empower your teammates with interactive learning.
And the best part? The browser extension is 100% free.
News from around the web
It's easy to think that Cybersecurity is a problem for big corporations, but it can be doubly so for small businesses, families, or individuals. In the UK, one in two small businesses experienced a cyberattack last year, and on average, they suffer four major attacks every week. So step into a free "cyber action toolkit" from the UK's National Cyber Security Centre. It offers simple and powerful guidance, which we will go over here. Starting with the baseline of two-factor authentication (2FA).
Two-step verification, also known as 2FA or multi-factor authentication (MFA), is an extra layer of security beyond just a password. When you log in, you must provide a second piece of information, like a code from your phone, to prove it's really you. Its effectiveness is staggering, creating a massive barrier against attackers. As the toolkit highlights: "two-step verification significantly reduces the likelihood of successful attacks between 76% and 99%". The toolkit mentions several types of 2FA, including codes sent via text message, authenticator apps (like Google or Microsoft Authenticator), and physical security keys (like a YubiKey).
Here is a fact that puts the modern password problem into perspective: the average internet user has 227 accounts requiring a password. This sheer volume makes it mentally impossible to follow the most basic security advice, using a unique and strong password for every single account. Reusing passwords across services is a gateway for attackers, but remembering hundreds of complex, random ones is beyond human capability.
This is why password managers are an essential tool. They solve the problem by creating, storing, and auto-filling strong, unique passwords for all your accounts, synchronised across your devices. The toolkit notes several types are available, including those built into your device (Apple, Google) or browser, as well as dedicated applications like Proton Pass.
Perhaps the most interesting advice, especially coming from a government source, is the proactive recommendation to actively manage and reduce your digital footprint. This goes beyond setting strong passwords and focuses on minimising the amount of information available for attackers to find and exploit in the first place.
The toolkit's actionable steps for this digital "tidying up" include:
Removing anything non-essential for your daily operations.
Asking others to remove outdated or excessive information about you.
Unlinking your profile from unknown or outdated connections on platforms like LinkedIn.
Keeping your personal and business accounts separate.
Making accounts private wherever possible.
Next, the NCSC advises that you create two separate user accounts on a computer, one for administration and one for daily use. If malware infects your day-to-day user account, it won't immediately have full administrative permissions to install malicious software, access core system files, or do deeper damage. The attacker would first need to find a way to escalate their privileges to the administrator account.
Now that you know these simple but powerful steps, what is the one change you will make today to protect your digital life?
Summary
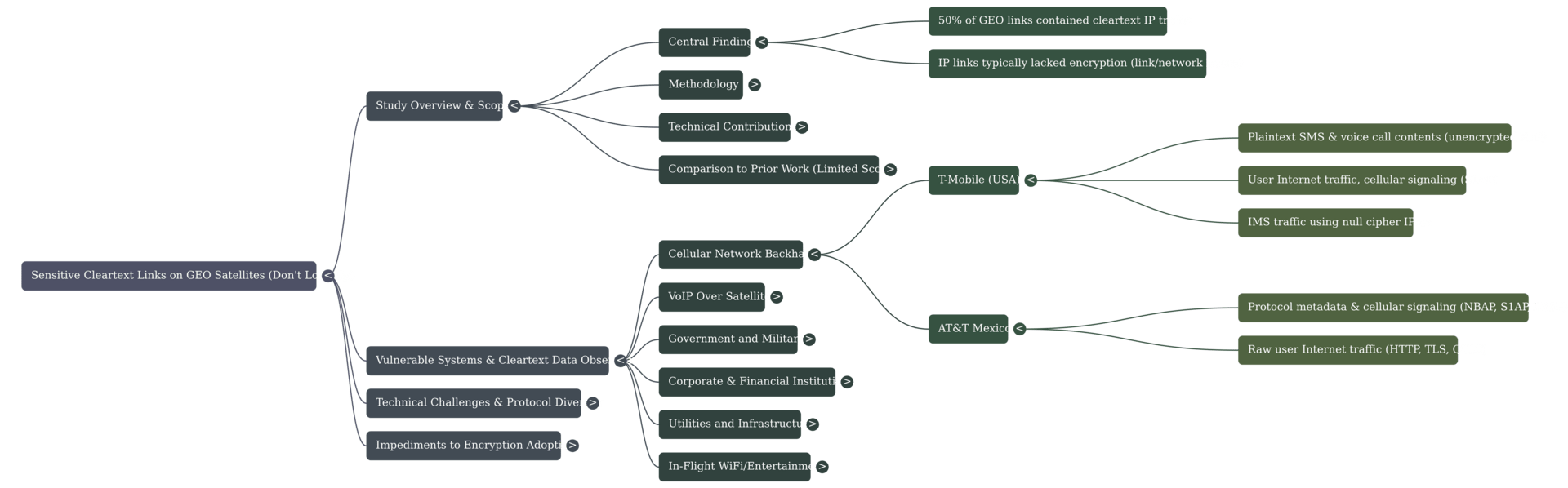
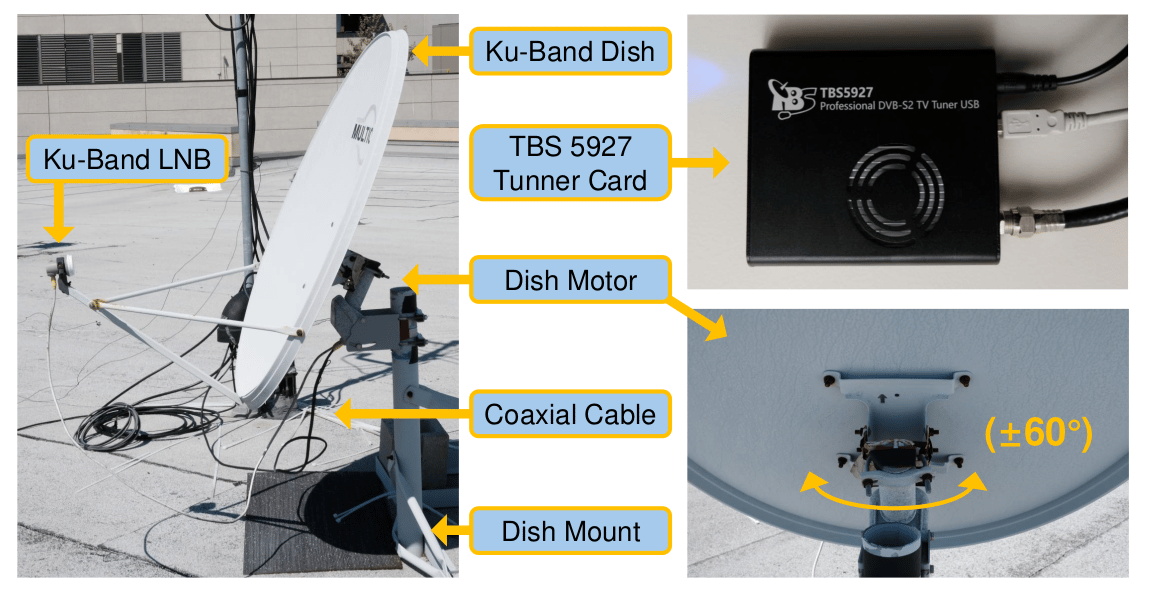
Researchers conducted the first comprehensive scan of IP traffic across 39 GEO satellites, overcoming technical challenges using low-cost, consumer-grade equipment to observe network security practices. This extensive study found that 50% of these GEO links contained unencrypted cleartext IP traffic, including sensitive data from utility control systems, military asset tracking, and cellular backhaul.
"We found 50% of GEO links contained cleartext IP traffic; while link-layer encryption has been standard practice in satellite TV for decades, IP links typically lacked encryption"
Geosynchronous (GEO) satellite links are the primary means for delivering reliable high-speed communication and IP backhaul to sensitive remote sites, serving utilities, government, military, and telecom users. Previous academic work on GEO infrastructure was narrowly focused, restricted to a few satellites, specific protocols, and struggled with decoding traffic due to poor signal quality. This led prior researchers to believe generalisations across the VSAT industry were nearly impossible due to the diverse, often proprietary protocols in use. The current study overcomes these challenges by using low-cost, COTS equipment to perform the first broad scan of 39 GEO satellites, demonstrating that wide-scale interception is feasible for low-resource attackers.
Use-case
GEO satellite links are the key method for providing IP backhaul and high-speed communication to remote, critical infrastructure, connecting thousands of GEO network links carried by hundreds of satellites. The sensitive, internal network exposed by the study includes unencrypted cellular backhaul, revealing cleartext call contents and metadata for providers like T-Mobile and AT&T Mexico. Furthermore, these links transport sensitive data for critical infrastructure, such as job scheduling for power grid repairs, military vessel tracking, and internal network traffic for banks, government, and large retail chains like Walmart-Mexico. These links are also leveraged to provide common consumer services, such as in-flight WiFi, where unencrypted metadata and audio streams were observed.
Future Work
The authors hope that this study will encourage future work providing greater visibility into satellite communications as critical network infrastructure. Clear directions for research include expanding scanning efforts to other frequency bands, such as Ka-band and C-band, which were not the focus of the current study. Future methodologies should also be developed for scanning different satellite orbits, such as Low Earth Orbit (LEO) systems. Finally, researchers should continue refining the protocol parsing stack to account for additional proprietary protocols and consider reverse-engineering satellite receivers for insights not available through passive black-box analysis.
You can download the paper here.