Dear Sentinels
So my wife and I have returned home after a lovely, though brief, holiday. She is still on holiday, but I am back to work, and with that said, we return to cybersecurity. Your details are online, publicly hacked, and free on the dark web! So the new Date Breach Observatory will have you believe, and I, for one, am happy with that. Proton’s new observatory, as in Proton Mail, has this down pat, with top-targeted sectors and data most often leaked. All of this is gained from the dark web, where criminals are actively selling your data. More on this in the article below.
In the academic article, I will be returning to the Internet of Things (IoT). I did my PhD in IoT, or at least a SysML dictionary focused on IoT. In this article, though, we will not be touching SysML and will instead be looking at a survey of Cybersecurity in IoT. With AI as a newish factor being drawn in.
Free email without sacrificing your privacy
Gmail is free, but you pay with your data. Proton Mail is different.
We don’t scan your messages. We don’t sell your behavior. We don’t follow you across the internet.
Proton Mail gives you full-featured, private email without surveillance or creepy profiling. It’s email that respects your time, your attention, and your boundaries.
Email doesn’t have to cost your privacy.
News from around the web
When we think of data breaches, we often picture massive corporations making front-page news. But this high-profile view conceals a much larger, more pervasive threat. The reality is that most breaches go unnoticed, creating a silent crisis that leaves businesses, especially smaller ones, greatly underestimating the risks they face. To shine a light on this hidden landscape, Proton has launched the Data Breach Observatory. By monitoring criminal sources directly on the dark web, this new tool bypasses official reports to reveal a more accurate picture of modern cyber threats.
A significant gap exists in our understanding of the cyber threat landscape because many organisations do not disclose breaches if they aren't legally required to. Fearing reputational damage, they often choose to stay silent. The Data Breach Observatory is designed specifically to fill this gap. It systematically monitors criminal sources on the dark web, identifying and verifying attacks as they are traded and discussed by threat actors. Proton's Director of Engineering, Eamonn Maguire, highlights the importance of this direct approach: "Many organisations choose not to disclose breaches when not legally required, or delay disclosure... Our Observatory fills this gap by monitoring criminal sources directly, meaning we can identify breaches regardless of whether the organisation affected chooses transparency."
While enterprise-level attacks capture the most attention, Proton's data reveals that hackers are overwhelmingly focused on smaller, more vulnerable targets. The Observatory found that small- and medium-sized businesses accounted for a staggering 70.5% of the breaches observed. This figure stands in stark contrast to the data for larger companies, which accounted for 13.5%, and enterprise organisations of more than 1,000+ employees, which accounted for the remaining 15.9%. Analysis of the most targeted sectors further sharpens this picture, with retail (25.3%), technology (15%), and media/entertainment (10.7%) topping the list.
Another common misconception is that hackers are only interested in highly sensitive financial data or government records. The Observatory's findings show that the most commonly leaked information is far more basic, yet incredibly valuable for malicious purposes.
Names and emails appear in 9 out of 10 breaches.
Contact data, such as phone numbers and addresses, was found in 72% of breaches.
Passwords were included in 49% of breaches.
While this seemingly simple information is the perfect fuel for phishing scams and unauthorised network access, it's not the whole story. Highly sensitive data, such as government IDs and health records, still appeared in 34% of the breaches analysed, proving that even hidden attacks on smaller targets can have devastating privacy consequences.
Simply scraping the dark web for data is not enough. Information from criminal sources is often unreliable, duplicated, or intentionally inflated. For instance, ransomware leak blogs routinely exaggerate their claims, which can lead to misleading statistics. Proton takes a deliberate, analytical approach to ensure accuracy. The Observatory focuses only on attacks targeting lone organisations and excludes massive, aggregated "infostealer dumps" that would skew the numbers. Furthermore, Proton partners with Constella Intelligence to apply multiple validation layers before disclosing a breach. These methods include cross-referencing data against known breach patterns, conducting metadata examination of timestamps and file structures, and performing direct company outreach to confirm incidents.
Now that we can see the full picture of who is being targeted and how, what is the one crucial security step your business has been overlooking?
Summary
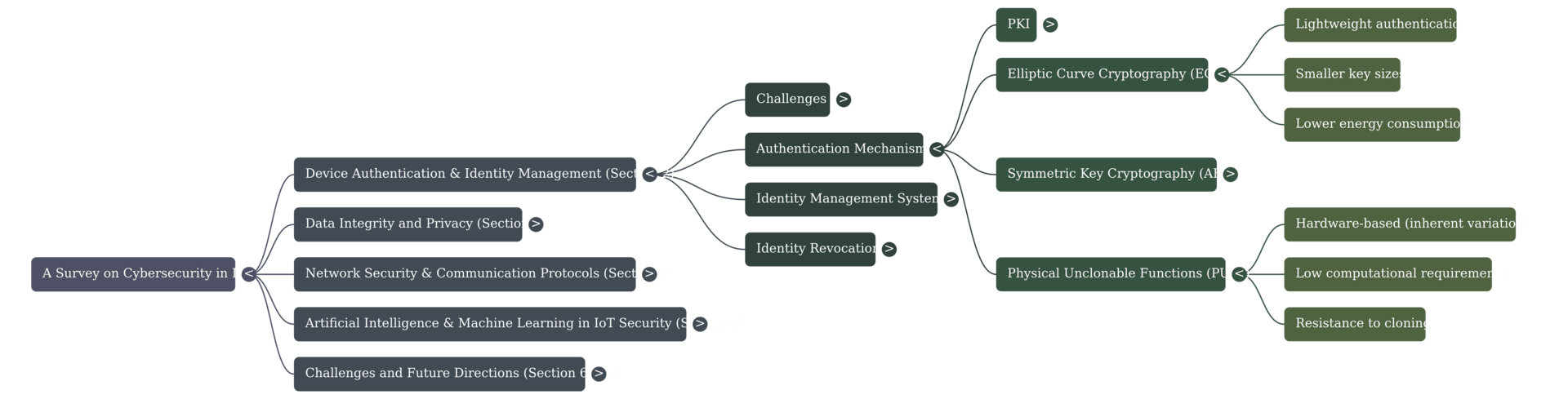
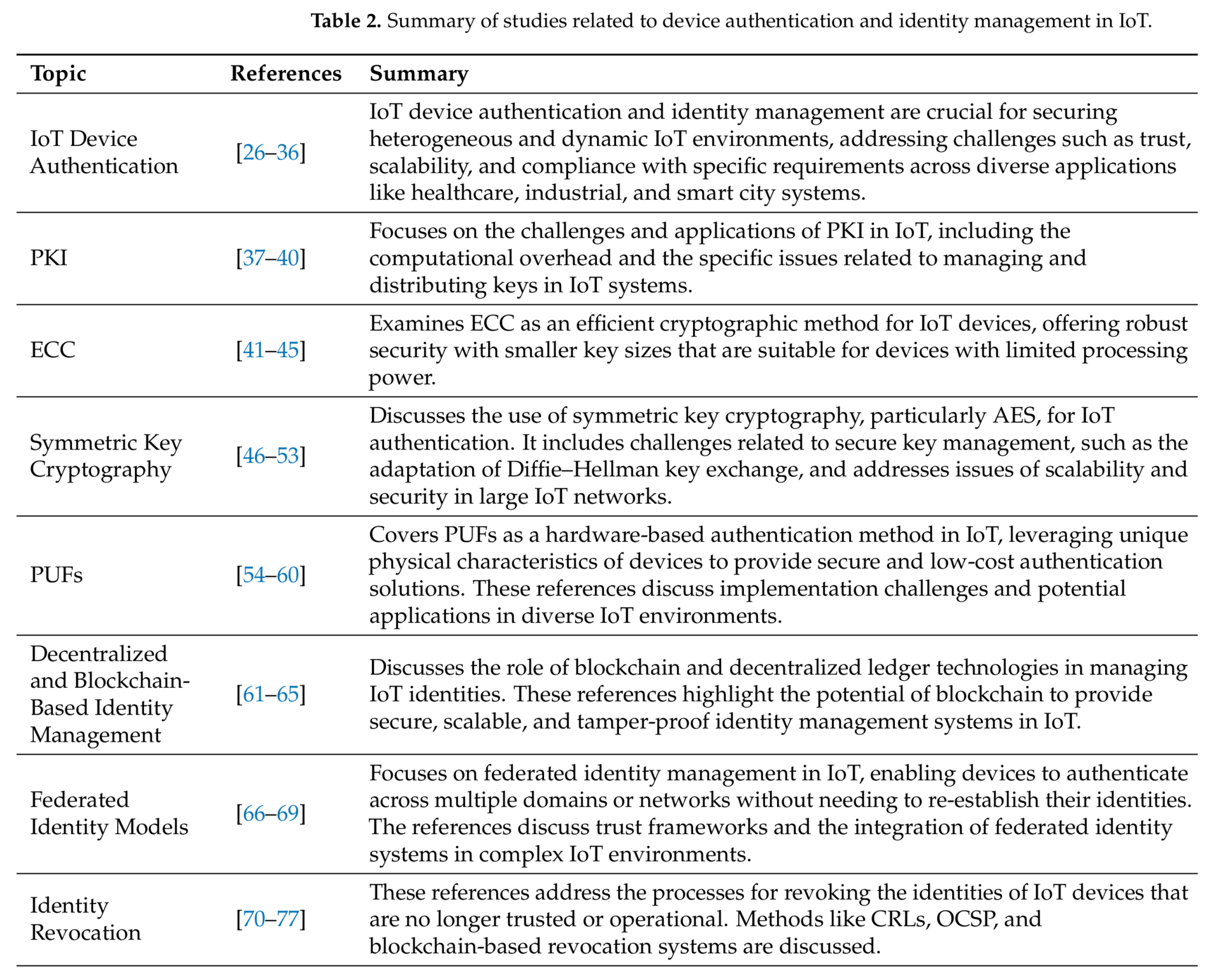
This paper presents a comprehensive survey of cybersecurity in the Internet of Things ecosystem, investigating the current research status and identifying critical security vulnerabilities. The survey also explores advanced strategies for threat mitigation, encompassing device authentication, data integrity, privacy, network security, and the emerging role of AI in defence.
Background
The proliferation of the Internet of Things (IoT) has fundamentally transformed the digital landscape, enabling a vast array of interconnected devices to communicate and share data seamlessly. However, the same characteristics that make IoT powerful (its distributed nature, device heterogeneity, and pervasive connectivity) also introduce unprecedented cybersecurity challenges. Unlike traditional IT systems, IoT networks consist of diverse devices, ranging from servers to resource-constrained sensors, often operating in untrusted environments. Many of these devices are designed with minimal security features due to cost or computational constraints, leaving them susceptible to various cyber threats. The consequences of security vulnerabilities can range from the compromise of individual devices to catastrophic, large-scale disruptions in critical infrastructure sectors like healthcare, energy, and transportation. In response, the field has seen a surge in research efforts focused on developing lightweight cryptographic methods, decentralised security models like blockchain, and AI applications to enhance threat detection.
Use-case
The IoT is driving innovation across various sectors, enabling seamless connectivity that leads to enhanced operational efficiency, reduced costs, and the creation of new business models. Key application areas span critical domains such as smart healthcare, where device authentication must adhere to stringent privacy regulations like HIPAA. Industrial IoT (IIoT) demands real-time protection mechanisms to secure critical operational data and prevent downtime in predictive maintenance processes. Furthermore, smart city applications require scalable identity management to handle dynamic additions and removals of devices, such as connected traffic lights and environmental sensors. Specialised protocols like LoRaWAN are critical for use cases in smart agriculture, logistics, and urban infrastructure due to their long-range, low-power capabilities. Even autonomous vehicles require ultra-low-latency communication systems to ensure safe navigation and resilience against cyberattacks on their sensor and control systems.
Future Work
Future research must prioritise the development of interoperable and scalable security frameworks to overcome the current lack of standardised security protocols across diverse IoT ecosystems. Addressing the exponentially growing attack surface necessitates a critical shift toward more proactive and adaptive security strategies, including managing the new risks introduced by adversarial attacks on AI models. There is a pressing need to focus on the scalability of all security solutions, from cryptographic and authentication mechanisms to managing large, distributed IoT networks. Techniques like Distributed Ledger Technology (DLT) offer promising avenues for achieving decentralised and scalable security in the IoT environment. Furthermore, future research should explore innovative business models and cost-effective security solutions to incentivise investment in robust protection, while also addressing the critical human factor through user awareness and education.
You can download the article here.


